 Security researchers from around the web are reporting finding an increasing number of instances of proof of concept (PoC) code that incorporates the recently discovered Spectre and Meltdown vulnerabilities.
Security researchers from around the web are reporting finding an increasing number of instances of proof of concept (PoC) code that incorporates the recently discovered Spectre and Meltdown vulnerabilities.
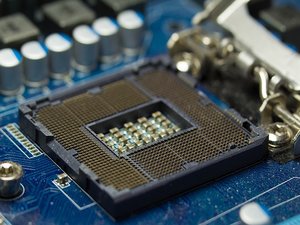
If you somehow missed those earlier reports, Spectre and Meltdown are a pair of critical security flaws recently discovered in literally every Intel chip set made over the last decade. Exploiting these vulnerabilities would give a hacker root-level access to the impacted system.
Since the discovery, the chip giant has been scrambling to fix the issue. However, their first attempt to do so caused so many system problems for people who installed the patch that the company is now recommending that users avoid it until they can come up with a better solution.
Unfortunately, that leaves you between the proverbial rock and a hard place. Installing the patch will protect you, but cause you to experience system reboots several times a day and seriously degraded performance. Not installing it leaves you at the mercy of the hackers.
So far, at least, it appears that most of the proof of concept code found is the result of security researchers playing with the exploits. This includes testing them, seeing how they work, and how to prevent them. That said, the researchers point out that it's all but certain that some of the PoC examples were created by teams of hackers who plan to use them in their next round of attacks.
To make matters worse, Mozilla has confirmed that the Spectre flaw can be executed remotely by inserting commands into Javascript. Given that, plus the increased appearance of PoC code fragments, it seems it's just a matter of time before we see the first ever Spectre-based hack. The clock is ticking.


